Beginning Electronic Discovery — Considering the Basics
When might a legal case involve extensive discovery, including electronic discovery (e-discovery)?
Suppose you sue a corporation and want to obtain documents/data (Request to Produce), information from the corporation itself (Interrogatories) and information from employees of the corporation (depositions). What might the subject matter of the lawsuit involve:
- Breach of contract or agreement
- Trademark or patent infringement
- Shareholder derivative action
- Product defect
- Defective drugs
When offices were filled with file cabinets and typewriters, where documents were located and “who knew what” was a little easier to determine. Typically, the documents were kept in one or maybe two central locations and the dissemination to multiple people was more difficult, so “who knew what” was usually a smaller crowd than today.
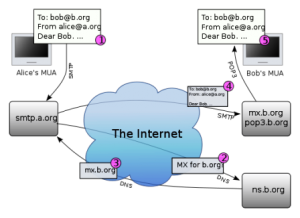
Today, the life of a single email may span dozens or hundreds of potential recipients. It may be forwarded to even more and many replies might be generated to some or the popular “reply all” of the people included in the initial email. A scanned piece of correspondence might be seen by multiple users through a document management system and distributed to even more through email. Some users may have deleted their email; the email may have been saved by some users; or the network archive system may have maintained the only version of the email in existence.
Because of the prolific nature of today’s methods for communicating and storing information, the methods employed to approach litigation discovery has changed dramatically. Today, parties have a need to understand more about the ways and methods of operation of their adversaries than they did when we just had to go to the “file room” to find the relevant documents.
We need to think about things like “data maps”, identifying custodians and data management. We need to understand how our adversary maintains their documents and data. We need to know what individuals were involved in the subject matter (and often collateral subjects) and are likely to have documents or data that may or may not be in possession of other “record custodians”.
So, where can you start if you need to know what the ABC Corporation knew and knows in connection with a given matter or subject?
Although the Florida Rules of Civil Procedure are not nearly as efficient for conducting e-discovery as the Federal Rules of Civil Procedure, discovery is still the way to obtain the information you need. For example, you might ask the opposing party if they have a “data map” or a “data reference model”. What a data map is can vary from one person or company to another; so, it is important to carefully review it and determine what, if any, important information it gives. Effectively, a data map will set forth the location of all data in a given system or systems and the flow of that data through the system(s); it can be highly detailed and complex or very basic. Although data maps can be useful tools, know that they are typically very time consuming and expensive to pu together; so do not be surprised if the company says they do not have one.
Who manages the overall data and documents for the corporation? In most companies, that person is going to be called something like the Information Technology Manager, the IT Supervisor, the VP of Information Services or any number of variations. This is a person who should understand:
- How the computer systems are set up.
- How information moves through the company in general.
- Who has access to what information?
- What policies exist for computer usage in the company?
- Where is information stored?
- How is the information stored?
- What are the company’s data/information retention policies?
Under the federal rules, the parties are compelled to have a Rule 26(f) “meet & greet” to discuss discovery in general and e-discovery in specifics. If the lawyer for the ABC Corporation is incapable of satisfying all the information you believe you need to know about the company’s IT structure, ask for a 30(b)(6) deposition of the IT Supervisor.
During the Rule 26 “meet & greet” conference and/or from the Rule 26(A)(1)(c) initial disclosures, the primary records custodians should be able to be identified and agreements hopefully reached on whether to limit the number of custodians from whom documents will be initially collected or to agree on the specific custodians. Why limit the number of custodians? For example, if the respective lawyers have disagreement over the extent of records custodians, a sample collection might be agreed upon in order to try and resolve that disagreement. In addition, both parties’ attorneys may agree they need to do a sampling in order to mutually determine who the relevant record custodians may be.
This is a good time to also try and determine whether extreme preservation efforts should be made. Individual custodian computers may need to have forensic mirror images created of them for example. If the custodian needs to continue to use a laptop, this is a good way to preserve what is on it and accommodate the uninterrupted business practice of the custodian. A forensic mirror image of a hard drive is not simply a copy of a hard drive. The image must be created without altering any data or metadata on the computer. This is a process best left to forensic experts.
In our next installment, we will discuss the various methods of document and data collection, processing, culling and producing.
Share This